Category: Security
-

When security & sustainability meet: don’t try to change user behavior
Security purists are as bad as the sustainability ideologues, and they don’t help anyone.
-

Roman Climate Optimum and energy system resiliency
It’s quite easy to argue that modern civilization is much more robust and resilient than any ancient society, but consider how much of our critical infrastructure is written in memory unsafe languages!
-

How do you access knowledge without electricity?
Nationwide systems failure of the electricity transmission grid is unlikely, but what are the risks? What happens in a black start? Could space weather cause data loss? How do you access knowledge without electricity?
-
Configuring for security, privacy and convenience
Balancing security, privacy and convenience is not easy. I’ve spent quite a lot of time figuring out how to configure my various computer systems with this goal in mind. Computers are supposed to make our lives more convenient and you sometimes have to trade privacy for convenience e.g. Outlook processing…
-

Should companies be required to publish security reviews?
Many incidents of fraud occur not through cards being physically stolen, but through breaches in security at the shops we buy products from. Should companies be required to publish security reviews?
-

Email is not a good database
Email is insecure. Anything of any importance should be saved somewhere else. It’s not a good database, so shouldn’t be treated like one.
-

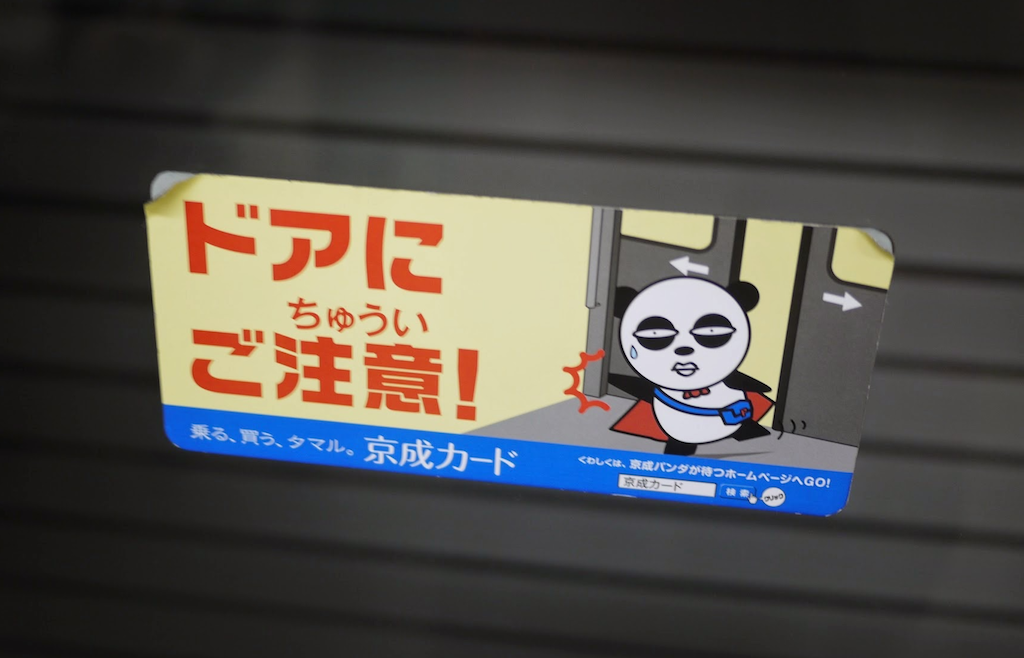
Cyber security and leaving the door unlocked
When it comes to insurance, it’s the same as locking up and installing an alarm
-

We’re still in v1.0 of the cyber security industry
Unlimited attack surfaces. Users not paying attention to basic security practices. Vague vendor promises. It looks like a very immature landscape where things are just getting started.
-

The state of secure, encrypted messaging
Everyone should have an expectation of being able to communicate with someone else in a verifiably secure manner.
-

Home Office Investigatory Powers regulations consultation response on encryption backdoors
This is my response to the UK Home Office consultation on the Draft Investigatory Powers (Technical Capability) Regulations 2017.